Hidden Data Risks: The ITAD Oversights That Put Your Business at Risk
Are You Really Destroying All Data? Most Companies Aren’t.
Every company handling end-of-life IT equipment has a top requirement—secure equipment disposal. Yet, even the most diligent organizations routinely miss hidden data-bearing devices, exposing themselves to serious security risks. Hard drives, SSDs, and even embedded storage in modern electronics are often missed, leaving sensitive information vulnerable to breaches. Gartner research indicates that a considerable percentage of IT assets, around 30%, can be lost or unaccounted for. This “loss” can manifest in various ways, including physical loss, misplacement, or “ghosting” (assets that are active but not tracked).
The Hidden Data Risks Lurking in Your IT Assets
Even security-conscious organizations fail to account for all data storage devices. Here are real-world examples of how missed hard drives and other storage media can lead to serious vulnerabilities:
- Governmental Vulnerabilities: Securis found Top Secret diagrams for a key U.S. Government building mixed in with discarded items during a routine electronics recycling pickup. Without thorough IT asset disposition (ITAD) procedures, this could have led to a catastrophic security breach.
- Financial Industry Oversights: A financial services company, confident in its IT asset management, had already shredded its own drives. Yet, Securis’ triple-check process found an unaccounted-for storage drive hidden in a copier—a device often overlooked as a data risk as well as three additional items that were not in the companies inventory list. These overlooked assets could have led to a major compliance failure.
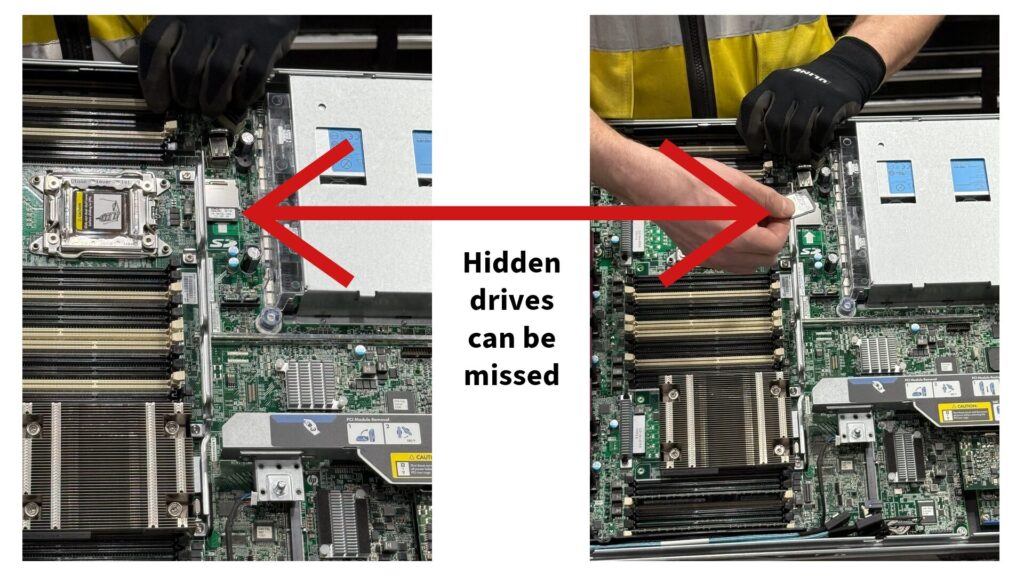
- Server Room Blunders: Another financial services client assured Securis that all hard drives had been removed from eight decommissioned server cabinets. Upon our close inspection, 86 drives (72 SSDs and 14 HDDs) were discovered—a staggering 15% of the total drives assumed to have been removed.
- Telecom Mishaps: A major telecom company decommissioned 300 servers, claiming all storage had been stripped. Securis uncovered 30 overlooked hard drives—each containing potentially sensitive data.
Government Reports Confirm Data Disposal Failures
 The Office of the Inspector General (OIG) discovered that an FBI-controlled facility had classified and unclassified law enforcement data stored on pallets without adequate protection. If these items had been wiped or degaussed on-premises, there would have been at least one layer of protection before transportation took place.
The Office of the Inspector General (OIG) discovered that an FBI-controlled facility had classified and unclassified law enforcement data stored on pallets without adequate protection. If these items had been wiped or degaussed on-premises, there would have been at least one layer of protection before transportation took place. - A 2024 NRC OIG report recommended strengthening IT asset disposal processes, including updating decommissioning standards and enforcing strict inventory control.
- In a State of New Jersey audit, 79% of decommissioned state laptops planned for public auction were found to contain data.

Medical Devices: The Overlooked Data Risk
It’s not just traditional IT equipment—embedded storage in medical devices and equipment is often overlooked. A recent study found that 13 infusion pump devices still contained wireless authentication data when resold on secondary markets.
Accordingly, the Federal Register recently proposed a new rule to strengthen the cybersecurity of electronic protected health information. This proposed rule strengthens overall cybersecurity measures and supports the ongoing requirement for robust data destruction practices to protect ePHI.
How Securis Prevents Costly Mistakes
Securis’ Secure, Accurate, and Sustainable IT asset disposition approach ensures no storage device is left behind:
 Triple-Check Guarantee: Multi-step verification ensures hidden drives don’t slip through the cracks.
Triple-Check Guarantee: Multi-step verification ensures hidden drives don’t slip through the cracks.- Separation of Duties: Independent verification eliminates single points of failure.
- NAID-Certified Hard Drive Shredding & Data Wiping: Securis ensures 100% data destruction with documented proof, whether on-site or off-site.
Choosing the Right ITAD Partner: What to Look For
Who you choose as your IT asset disposal partner matters. Securis helps companies avoid costly data breaches by ensuring every data-bearing device is identified and destroyed. Some best practices you can use to choose a vendor include:
- Certifications: Does the vendor have NAID AAA Certification for on and off-site destruction?
- Nationwide Coverage: Can they collect and process IT assets from multiple locations?
- Experience: Nothing can replace experience. Experienced vendors know where to look for hidden storage devices.
 Capabilities: Can the vendor perform shredding to required destruction standards for various assets and storage media types? Do they provide a strong chain of custody and certificates of destruction?
Capabilities: Can the vendor perform shredding to required destruction standards for various assets and storage media types? Do they provide a strong chain of custody and certificates of destruction?
Secure Your IT Assets Today
Don’t risk a data breach by overlooking hidden storage devices. Securis ensures 100% secure IT asset disposal with industry-leading ITAD services.
? Contact Securis today for a customized IT asset recycling and secure data destruction plan.