Data security has become a paramount concern for individuals and organizations in today’s digital environment. As we accumulate vast amounts of sensitive information on our hard drives, it’s crucial to understand the various methods available for securely destroying this data when it’s no longer needed. Let’s dive into the hard drive data destruction world and explore the techniques that ensure your confidential information doesn’t fall into the wrong hands.
The Importance of Proper Data Destruction
Before we delve into the specific methods, it’s worth emphasizing why proper data destruction is critical. A data breach can result in astronomical financial losses and irreparable damage to a company’s reputation. Taking a cavalier approach to data disposal is simply not an option. Whether you’re a large corporation or an individual looking to sell your old computer, ensuring your sensitive data is completely and irretrievably destroyed before passing it on for re-use or recycling should be a top priority. Software-based wiping is one method for removing data from a hard drive, but it may not be adequate for all situations. When physical hard drive destruction is called for, the following are the best options:
 Degaussing: Erasing with Magnetic Force
Degaussing: Erasing with Magnetic Force
Degaussing is a fascinating process that uses powerful magnetic fields to scramble the data stored on magnetic media, such as hard drives and tape drives. When a degausser is applied to a hard drive, it changes the magnetic domains where the data is stored, effectively scrambling the information into random patterns. This renders the data on the drive wholly unreadable and unrecoverable.
Key Points About Degaussing:
- Degaussing is effective on both functional and non-functional drives
- Degaussing a hard drive destroys not only data but also drive formatting and control information
- Degaussing is a process that renders the drive permanently unusable
- Degaussing is compliant with many stringent data destruction standards
NSA-Approved Equipment
For the highest level of security, organizations like Securis use NSA-approved degaussers, such as the LM4 model. These machines are recertified annually to ensure they meet the most rigorous standards for data destruction.
 Shredding: Crushing the Problem
Shredding: Crushing the Problem
Nothing beats the physical destruction of the hard drive when it comes to absolute certainty in data destruction. Hard drive shredding is precisely what it sounds like – the drive is fed into an industrial shredder that reduces it to small metal fragments.
Benefits of Hard Drive Shredding:
- Provides visual confirmation of data destruction
- Extremely effective against all forms of data recovery
- Can be performed on-site for added security
The Hard Drive Shredding Process
Typically, hard drive shredding involves the following steps:
- Collection and inventory of drives
- Secure transport (if shredding is not performed on-site)
- Shredding using industrial-grade equipment
- Proper disposal or recycling of the resulting materials
 MicroShredding: Taking It a Step Further
MicroShredding: Taking It a Step Further
Microshredding (also known as disintegration) takes the shredding process to the extreme for those requiring an even higher level of security. This method reduces hard drives to dust-like particles, ensuring that no readable data can possibly survive.
When to Consider MicroShredding:
- Handling classified or top-secret information
- Dealing with highly sensitive personal or financial data
- Compliance with the most stringent data destruction regulations
Combining Methods for Ultimate Security
While each method can be effective independently, many data destruction services combine techniques for added peace of mind. For instance, a common approach is to degauss hard drives before shredding them. This two-step process ensures that the data is first magnetically erased and then physically destroyed, leaving no possibility of recovery.
 Choosing the Right Method for Your Needs
Choosing the Right Method for Your Needs
Selecting the appropriate data destruction method depends on several factors:
Security Requirements
Consider the sensitivity of your data and any regulatory compliance needs. Physical destruction methods like shredding or micro shredding may be necessary for sensitive or highly classified information.
Volume of Drives
If you’re dealing with a large number of drives, a method like degaussing might be more efficient than individual wiping.
Drive Condition
Remember that wiping requires a functional drive, while degaussing and shredding can be performed on non-operational devices.
 The Role of Professional Data Destruction Services
The Role of Professional Data Destruction Services
While some data destruction methods can be performed in-house, many organizations opt to use professional services for several reasons:
Certified Equipment and Processes
Companies like Securis use NSA-approved equipment and follow strict protocols to ensure compliance with industry standards. They will also have essential certifications such as NAID AAA and R2v3, which can assure clients that the company meets rigorous standards for security and sustainability.
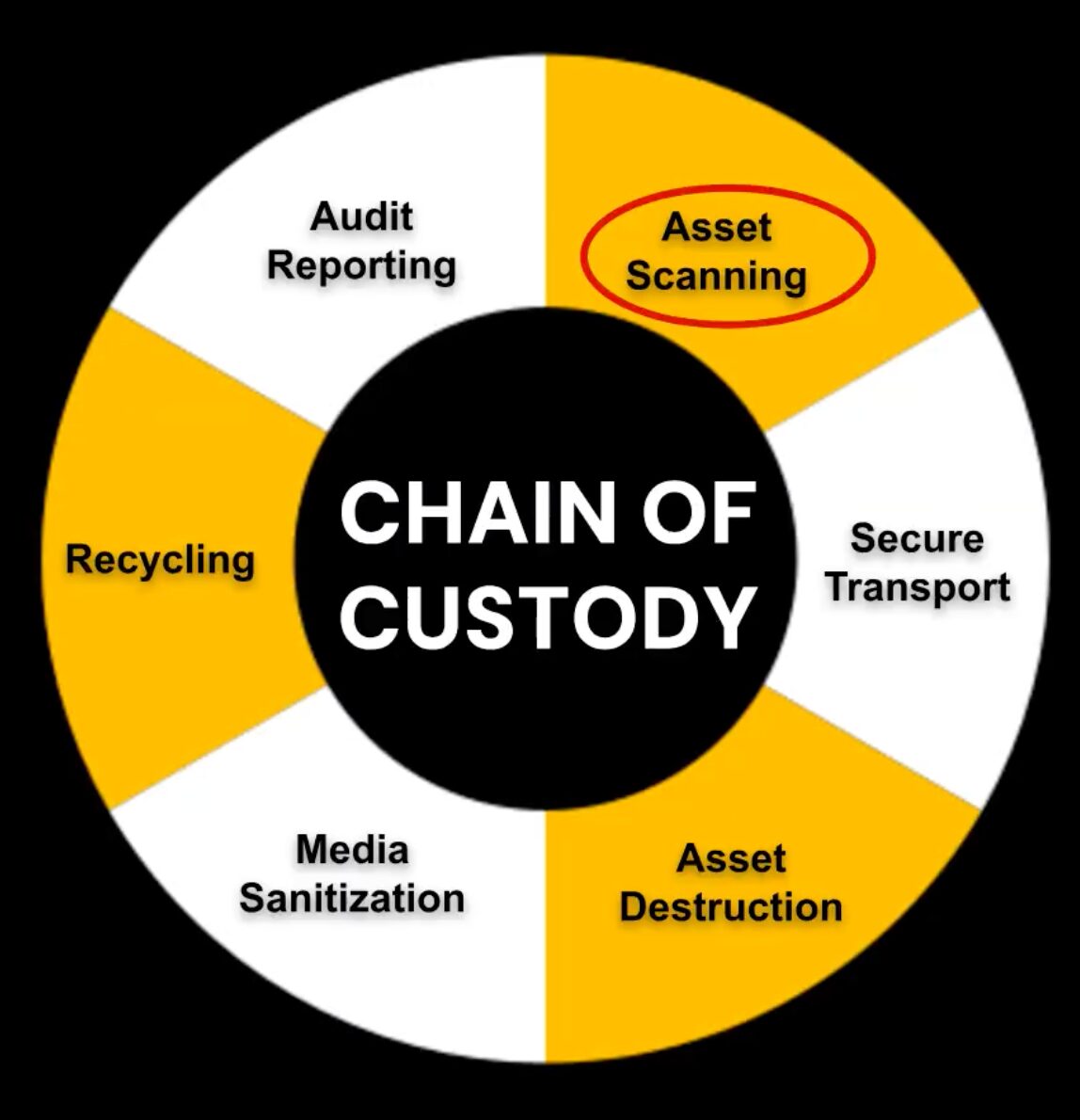
Chain of Custody
Professional services provide detailed documentation of the destruction process, which can be crucial for audit purposes.
On-Site Services
Many providers, including Securis, offer on-site destruction, eliminating the need to transport sensitive data off-premises and allowing secure data destruction to occur on-premises and under the client’s supervision.
Environmentally Responsible Disposal
Reputable data destruction companies ensure that materials are recycled or disposed of in an environmentally friendly manner. An R2v3 certification is an important way to know how serious the company is about sustainable recycling.
 Beyond Hard Drives: Other Media to Consider
Beyond Hard Drives: Other Media to Consider
While we’ve focused primarily on hard drives, it’s important to remember that data can reside on various media types. Professional data destruction services often handle:
- Solid State Drives (SSDs)
- Tape drives
- USB flash drives
- Mobile devices
- Optical media (CDs, DVDs)
Each of these may require specific destruction techniques to ensure complete data erasure. Because many of these devices are physically small, disintegration may be the best option for physical shredding.
 Conclusion: Taking Data Destruction Seriously
Conclusion: Taking Data Destruction Seriously
There are many vulnerabilities to a company’s data. These vulnerabilities are not over when the life of the data-bearing device is over. Protecting that data throughout its lifecycle—including its end-of-life—is crucial. Whether you choose wiping, degaussing, shredding, or a combination of methods, the key is approaching data destruction with the seriousness it deserves. Remember, proper data destruction costs are insignificant compared to the potential fallout from a data breach. By understanding and implementing appropriate data destruction methods, you’re not just protecting information – you’re safeguarding your organization’s future, reputation, and peace of mind. So, the next time you’re faced with old hard drives or other data-bearing devices, don’t just toss them in the trash or let them gather dust in a closet. Take the time to ensure your sensitive data is genuinely, irrevocably destroyed. After all, in data security, it’s always better to be safe than sorry.

















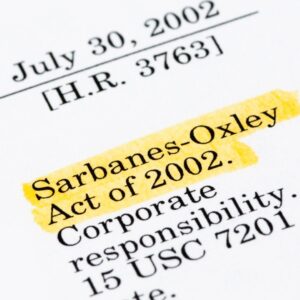 SOX was enacted in response to major corporate scandals like Enron and WorldCom to increase transparency in financial reporting and hold companies accountable for their financial practices. Key provisions include:
SOX was enacted in response to major corporate scandals like Enron and WorldCom to increase transparency in financial reporting and hold companies accountable for their financial practices. Key provisions include:





 The Responsible Recycling (R2v3) certification is a globally acknowledged electronics recycling and refurbishment standard. Developed by
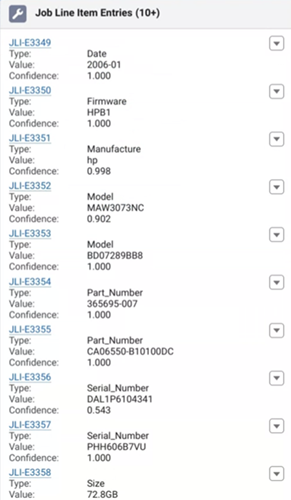
The Responsible Recycling (R2v3) certification is a globally acknowledged electronics recycling and refurbishment standard. Developed by  One of the primary concerns in asset disposition is ensuring data security in ITAD.
One of the primary concerns in asset disposition is ensuring data security in ITAD.  Many companies have corporate social responsibility (CSR) considerations to fulfill. They must adhere to electronic waste disposal standards and e-waste legal regulations, ensuring that hazardous material disposal is properly managed. They must also implement best practices for recycling electronic waste that maximize material recovery and reuse, and minimize landfill use. Making headlines for
Many companies have corporate social responsibility (CSR) considerations to fulfill. They must adhere to electronic waste disposal standards and e-waste legal regulations, ensuring that hazardous material disposal is properly managed. They must also implement best practices for recycling electronic waste that maximize material recovery and reuse, and minimize landfill use. Making headlines for  Partnering with an R2v3 certified recycler enhances a company’s reputation by demonstrating a commitment to responsible e-waste management. This builds trust with customers, stakeholders, and employees and aligns with corporate social responsibility (CSR) initiatives.
Partnering with an R2v3 certified recycler enhances a company’s reputation by demonstrating a commitment to responsible e-waste management. This builds trust with customers, stakeholders, and employees and aligns with corporate social responsibility (CSR) initiatives.  R2v3-certified companies follow standardized and transparent processes for e-waste management compliance. This includes thorough documentation and reporting, which is essential for auditing and tracking purposes. Strict chain of custody controls and downstream due diligence documentation is required, including the tracking of all electronic materials from receipt to final disposition, documentation of downstream recycling partners and their practices as well as verification of final material disposition.
R2v3-certified companies follow standardized and transparent processes for e-waste management compliance. This includes thorough documentation and reporting, which is essential for auditing and tracking purposes. Strict chain of custody controls and downstream due diligence documentation is required, including the tracking of all electronic materials from receipt to final disposition, documentation of downstream recycling partners and their practices as well as verification of final material disposition.  By partnering with an R2v3-certified recycler, companies can also realize economic benefits. R2v3 certified recyclers must efficiently recover valuable materials from e-waste, which can be refurbished and resold, thus reducing the overall cost of asset disposition. Having an R2v3 certification supports a circular economy, meaning that a vendor will ensure that all devices are used as long as possible, and then when devices can no longer be used, refurbish electronic devices and their components wherever possible. At the true end of life, a circular economy means recovering materials so they can become part of something new, whether that’s a new electronic device or something entirely different.
By partnering with an R2v3-certified recycler, companies can also realize economic benefits. R2v3 certified recyclers must efficiently recover valuable materials from e-waste, which can be refurbished and resold, thus reducing the overall cost of asset disposition. Having an R2v3 certification supports a circular economy, meaning that a vendor will ensure that all devices are used as long as possible, and then when devices can no longer be used, refurbish electronic devices and their components wherever possible. At the true end of life, a circular economy means recovering materials so they can become part of something new, whether that’s a new electronic device or something entirely different. 
 Key Factors in Choosing a Secure and Responsible IT Asset Disposition (ITAD) Partner
Key Factors in Choosing a Secure and Responsible IT Asset Disposition (ITAD) Partner
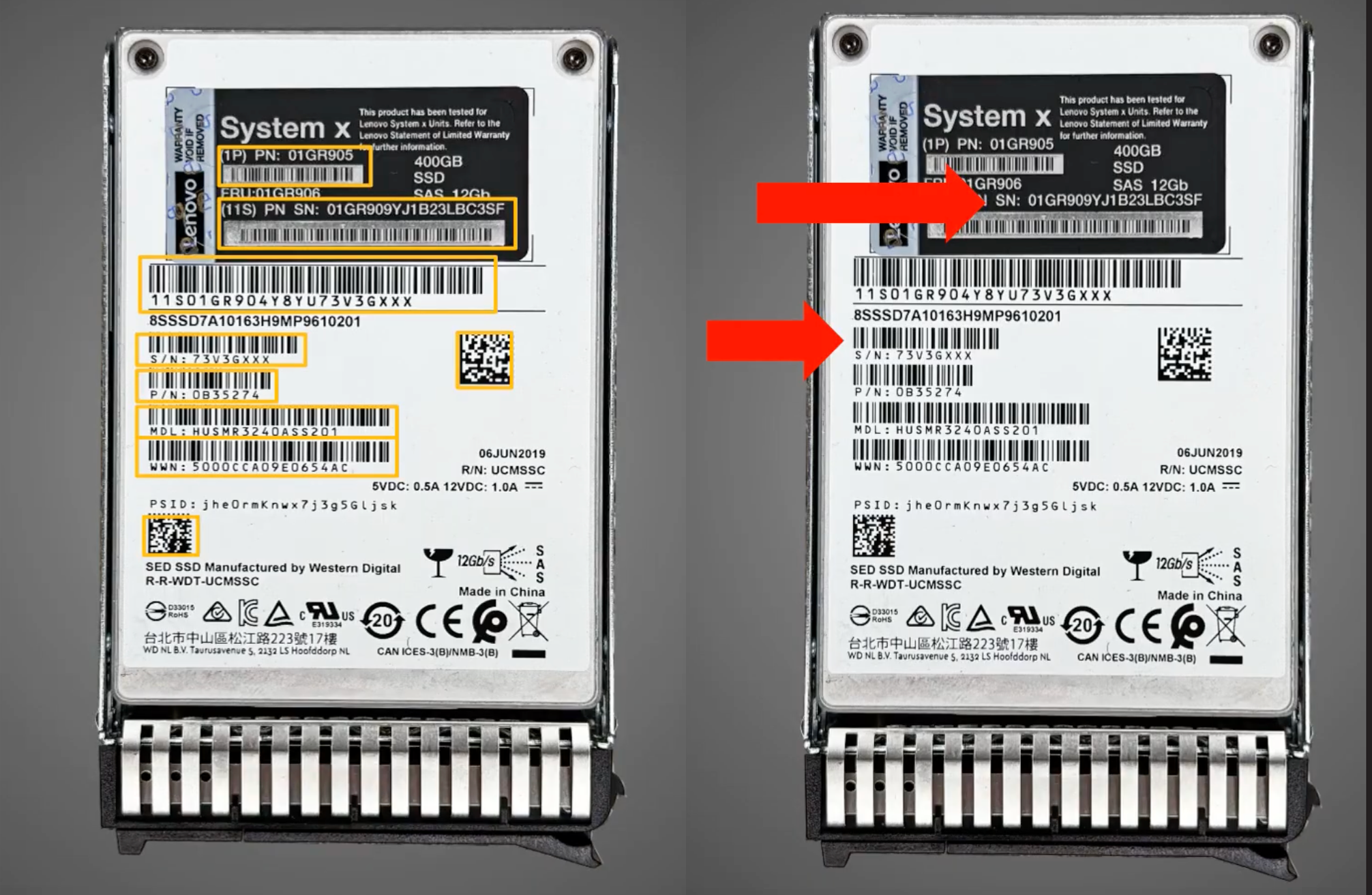
 Transparency is a crucial indicator of a responsible e-waste partner. Ideally, an ITAD partner should provide comprehensive and accurate reporting for the entire chain of custody. Ensure your chosen vendor:
Transparency is a crucial indicator of a responsible e-waste partner. Ideally, an ITAD partner should provide comprehensive and accurate reporting for the entire chain of custody. Ensure your chosen vendor:
 Beyond security, accuracy, and sustainability, consider the following factors.
Beyond security, accuracy, and sustainability, consider the following factors.